OK verstanden.
Code: Alles auswählen
#!/bin/sh
#####################################################
# IPTables Firewall-Skript #
# #
# erzeugt mit dem IPTables-Skript-Generator auf #
# tobias-bauer.de - Version 0.4 #
# URL: http://www.tobias-bauer.de/iptables.html #
# #
# Autor: Tobias Bauer #
# E-Mail: scripts@tobias-bauer.de #
# #
# Das erzeugte Skript steht unter der GNU GPL! #
# #
# ACHTUNG! Die Benutzung des Skriptes erfolgt auf #
# eigene Gefahr! Ich übernehme keinerlei Haftung #
# für Schäden die durch dieses Skript entstehen! #
# #
#####################################################
# iptables suchen
iptables=`which iptables`
# wenn iptables nicht installiert abbrechen
test -f $iptables || exit 0
case "$1" in
start)
echo "Starte Firewall..."
# alle Regeln löschen
$iptables -t nat -F
$iptables -t filter -F
$iptables -X
# neue Regeln erzeugen
#$iptables -N garbage
#$iptables -I garbage -p TCP -j LOG --log-prefix='[Drop-TCP]' --log-level 4
#$iptables -I garbage -p UDP -j LOG --log-prefix='[Drop-UDP]' --log-level 4
#$iptables -I garbage -p ICMP -j LOG --log-prefix='[Drop-ICMP]' --log-level 4
#$iptables -A INPUT -s 192.168.111.0/24 -j LOG --log-prefix='[netfilter] ' --log-level 4
$iptables -A INPUT -s 10.8.0.0/24 -j LOG --log-prefix='[netfiltervpn] ' --log-level 4
# Default Policy
$iptables -P INPUT DROP
$iptables -P OUTPUT DROP
$iptables -P FORWARD DROP
# über Loopback alles erlauben
$iptables -I INPUT -i lo -j ACCEPT
$iptables -I OUTPUT -o lo -j ACCEPT
#####################################################
# ausgehende Verbindungen
# Port 21
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 21 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 21 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 49152:65535 --dport 20 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 20 --dport 49152:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 22
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 22 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 22 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o tun0 -p TCP --sport 1024:65535 --dport 22 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i tun0 -p TCP --sport 22 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 25
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 25 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 25 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 53
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 53 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 53 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p UDP --sport 1024:65535 --dport 53 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p UDP --sport 53 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 80
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 80 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 80 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o tun0 -p TCP --sport 1024:65535 --dport 80 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i tun0 -p TCP --sport 80 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 110
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 110 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 110 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 123
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 123 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 123 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p UDP --sport 1024:65535 --dport 123 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p UDP --sport 123 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 143
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 143 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 143 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 443
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 443 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 443 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 465
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 465 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 465 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 993
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 993 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 993 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 995
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 995 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 995 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 1863
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 1863 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 1863 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 3306
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 3306 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 3306 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 5190
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 5190 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 5190 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 5050
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 5050 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 5050 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 5222
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 5222 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 5222 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 6667
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 6667 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 6667 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 9898
$iptables -I OUTPUT -o eth0 -p TCP --sport 1024:65535 --dport 9898 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 9898 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# ICMP
$iptables -I OUTPUT -o eth0 -p ICMP --icmp-type echo-request -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p ICMP --icmp-type echo-reply -m state --state ESTABLISHED,RELATED -j ACCEPT
#####################################################
# eingehende Verbindungen
# Port 21
$iptables -I INPUT -i eth0 -p TCP --sport 1024:65535 --dport 21 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 21 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 1024:65535 --dport 1024:65535 -m state --state NEW -j ACCEPT
$iptables -I INPUT -i eth0 -p TCP --sport 1024:65535 --dport 20 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 49152:65535 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 20 --dport 1024:65535 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
# Port 22
$iptables -I INPUT -i eth0 -p TCP --sport 1024:65535 --dport 22 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 22 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 22 aus VPN Netz erlauben
$iptables -A INPUT -i tun0 -s 10.8.0.3 -p tcp --dport 22 -m state --state NEW -j ACCEPT
# Port 80
$iptables -I INPUT -i eth0 -p TCP --sport 1024:65535 --dport 80 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 80 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -I INPUT -i tun0 -p TCP --sport 1024:65535 --dport 80 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o tun0 -p TCP --sport 80 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# Port 443
$iptables -I INPUT -i eth0 -p TCP --sport 1024:65535 --dport 443 -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p TCP --sport 443 --dport 1024:65535 -m state --state ESTABLISHED,RELATED -j ACCEPT
# ICMP
$iptables -I INPUT -i eth0 -p ICMP --icmp-type echo-request -m state --state NEW,ESTABLISHED,RELATED -j ACCEPT
$iptables -I OUTPUT -o eth0 -p ICMP --icmp-type echo-request -m state --state ESTABLISHED,RELATED -j ACCEPT
#####################################################
# Erweiterte Sicherheitsfunktionen
# SynFlood
$iptables -A FORWARD -p tcp --syn -m limit --limit 1/s -j ACCEPT
# PortScan
$iptables -A FORWARD -p tcp --tcp-flags SYN,ACK,FIN,RST RST -m limit --limit 1/s -j ACCEPT
# Ping-of-Death
$iptables -A FORWARD -p icmp --icmp-type echo-request -m limit --limit 1/s -j ACCEPT
#####################################################
# VPN Netz routen
$iptables -D FORWARD -i tun0 -o eth0 -s 10.8.0.0/24 -d 192.168.111.0/24 -m conntrack --ctstate NEW,ESTABLISHED,RELATED -j ACCEPT
#####################################################
# bestehende Verbindungen akzeptieren
$iptables -A OUTPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
$iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
#####################################################
# Garbage übergeben wenn nicht erlaubt
#$iptables -A INPUT -m state --state NEW,INVALID -j garbage
#####################################################
# alles verbieten was bisher erlaubt war
#$iptables -A INPUT -j garbage
#$iptables -A OUTPUT -j garbage
#$iptables -A FORWARD -j garbage
;;
stop)
echo "Stoppe Firewall..."
$iptables -t nat -F
$iptables -t filter -F
$iptables -X
$iptables -P INPUT ACCEPT
$iptables -P OUTPUT ACCEPT
$iptables -P FORWARD ACCEPT
;;
restart|reload|force-reload)
$0 stop
$0 start
;;
*)
echo "Usage: $0 (start|stop)"
exit 1
;;
esac
exit 0
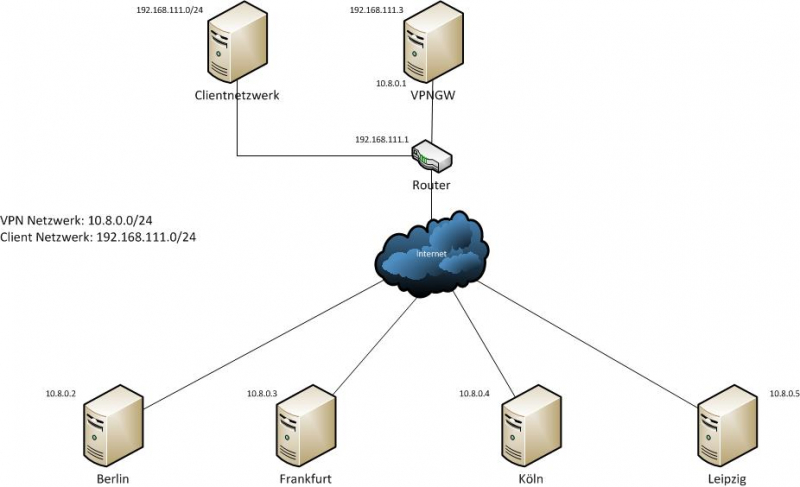
was momentan noch nicht geht, ich erreiche die Clients im VPN Netzt weder mit ping noch mit ssh aus dem normalen 192er netzt nicht.